Sponsored
 Textbooks.com
Textbooks.com
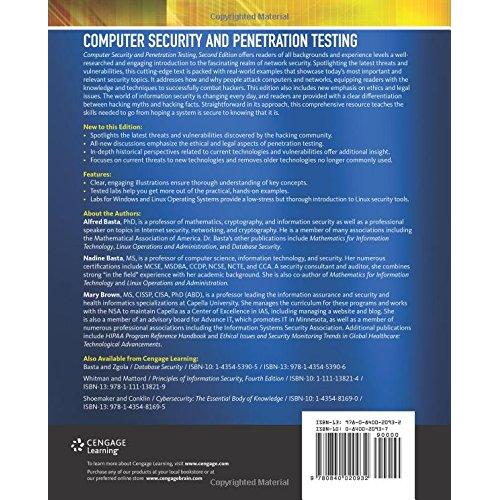
Course Technology, Inc. Computer Security and Penetration Testing
02-12-2024 23:16:42
| Brand | Cengage Learning |
| ASIN | 0840020937 |
| ISBN | 0840020937 |
| EAN | 9780840020932 |
| Author | Basta, Alfred |
| Book language | English |
| County of pub | Ashmore and Cartier |
| Dimensions | 25 cm xix, 376 pages : illustrations (black and white) |
| Edition | Second edition |
| Format | Paperback |
| Height | 231 mm |
| Imprint | Delmar |
| ISBN | 9780840020932 |
| Number of pages | xix, 376 |
| Publication date | 07 Sep 2013 |
| Published | 14/09/2013 |
| Publisher | Delmar Cengage Learning |
| Spine width | 20 mm |
| Weight | 688 g |
| Width | 189 mm |